In our previous article, I directed the eventlogs on 10.250.2.224 Windows Server 2019 with winlogbeat to the 5043 port of logstash running on Ubuntu Server 2019 with 10.250.2.222 ip address.
Configure Logstash to Read log files
In this article, I will configure logstash to read log files from winlogbeat and send to elasticsearch.
Let’s connect to our server running on 10.250.2.222 with ssh and switch to the /etc/logstash/conf.d/ directory and create a file named beats.conf and configure it as follows.
1 2 3 4 5 6 7 8 9 10 11 12 13 | root@logstash:~# cd /etc/logstash/conf.d/ root@logstash:/etc/logstash/conf.d# vim beat.conf input { beats {port => “5043”} } output { elasticsearch { hosts => [“10.250.2.221:9200”] index => “%{[@metadata][beat]}-%{+YYYY.MM.dd}” document_type => “%{[@metadata][type]” } } |
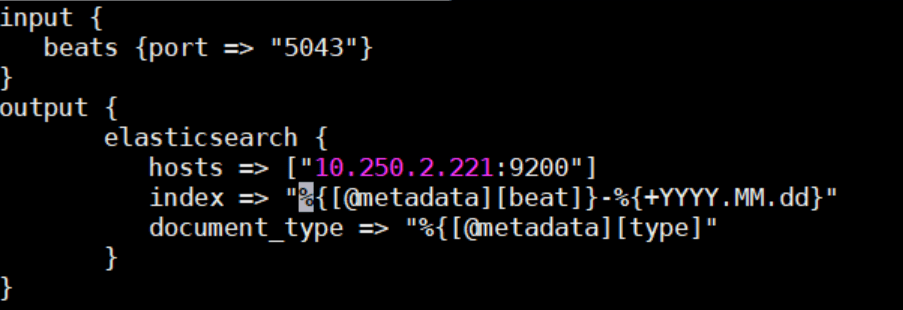
In the input section, we specify that logstash should listen to beats from port 5043.
In the output section, we enter the ip and port information of elasticsearh to which the logs will be sent.
With the index parameter, we specify that the data sent to elasticsearch will be indexed according to metadata and date.
With the document_type parameter, we specify that the document type sent to elasticsearch will be done according to the metadata, then we restart the logstash services.
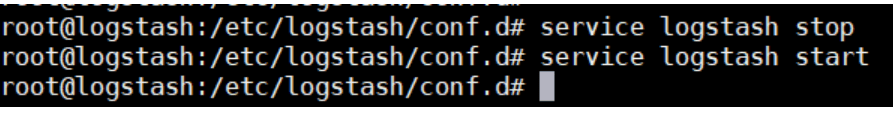
Start and Stop Logstash Service
1 2 | root@logstash:/etc/logstash/conf.d# service logstash stop root@logstash:/etc/logstash/conf.d# service logstash start |
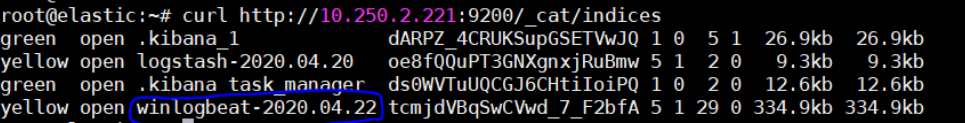
Now, data sent from winlogbeat to elasticsearch will start indexing in elasticsearch. When we connect to elasticsearch running on 10.250.2.221 and run the following command, we will list all the indexes on elasticsearch and we will see that the index winlogbeat-2020.04.22 has been created.
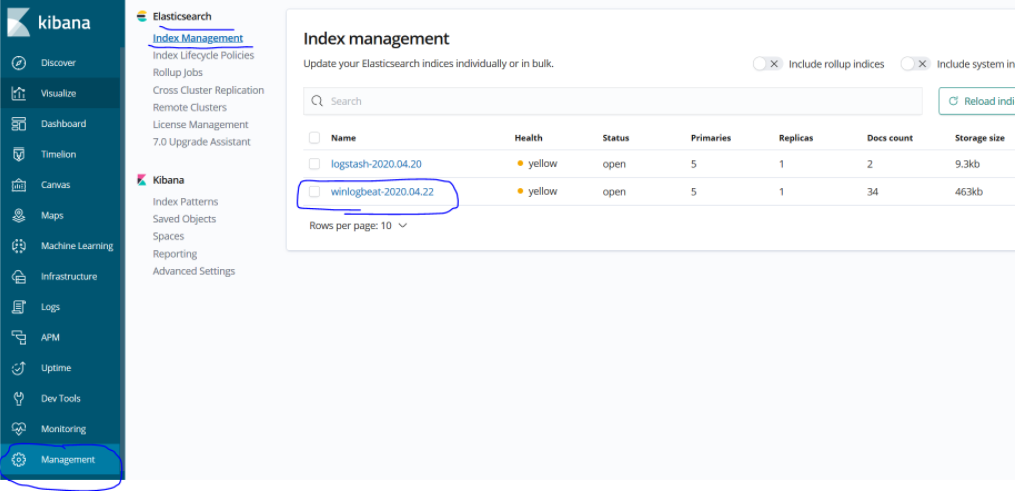
When we connect to the kibana service running on 10.250.2.223, we understand that this index has been seen by kibana and we are now ready to visualize the logs.
In the next article, we will create a dashboard for these logs that I have taken, on kibana..
You can read our other articles in this serie from the links below.
Install Elasticsearch on ubuntu server 19.10
Install Logstash on Ubuntu Server 19.10
Install Kibana on Ubuntu Server 19.10
Install Winlogbeat on Windows Server 2019
Configure Logstash to Read log files Windows
Create Kibana Dashboards For Windows Event Logs
![]()
 Database Tutorials MSSQL, Oracle, PostgreSQL, MySQL, MariaDB, DB2, Sybase, Teradata, Big Data, NOSQL, MongoDB, Couchbase, Cassandra, Windows, Linux
Database Tutorials MSSQL, Oracle, PostgreSQL, MySQL, MariaDB, DB2, Sybase, Teradata, Big Data, NOSQL, MongoDB, Couchbase, Cassandra, Windows, Linux 